The foundational keystone of a security ecosystem
A Root of Trust (RoT) underpins all Secure Operations on a chip and protects its critical assets. It provides a unique and unforgeable foundation from which a device builds its security architecture and authenticate each computing layer, from hardware to application. This is similar to our own unforgeable biometric identity, such as our fingerprints, from which other forms of identification can be rooted.
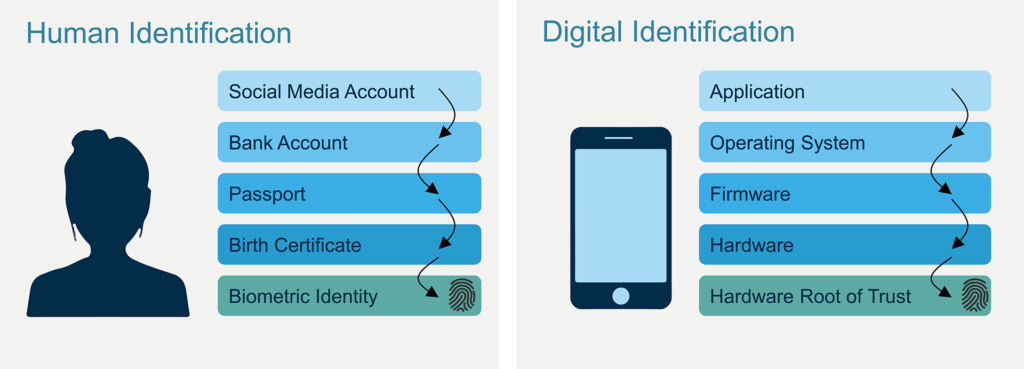
In a secure system, the RoT performs similar functions, provisioning and storing the cryptographic root key. This key is the basis for all secure operations, such as local on-device asset protection for identification, authentication, and secure communication with the external environment. As such, the RoT must always be trusted by the system and is best implemented as a Hardware Root of Trust (HRoT) for optimal protection.
As system security has evolved over time, it has been found that asset protection in layers, using both hardware and software, offers the best security. Hardware security is crucial for creating an isolated execution environment, enabling secure operations and internal memory management to be completed entirely in a “Hardware Secure Zone.”
Essential requirements to safely implement a Hardware Root of Trust onto a chip.
- Secure Root Key provisioning, ideally sourced from within the chip.
- Comprehensive protection of the stored Root Key from attempted attacks.
- Hassle-free integration with the device’s security ecosystem, including already installed crypto-engines, to provide a reliable foundation for all computing levels.
- Minimal additional process layers, as this can potentially add additional costs, lengthen the time-to-market, and increase threat vectors.
- Independently tested and verified by a 3rd party laboratory, such as Riscure, to provide certifiable protection.
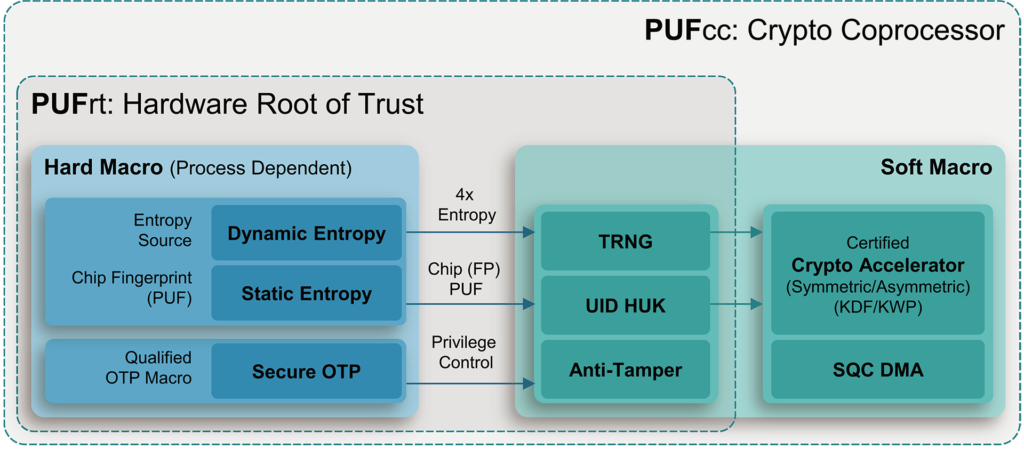
Sourcing the unique identifier (UID) and Hardware Unique Key (HUK) is a critical utilization of an HRoT. The UID is used for device identification and communication with other system components. As such, it must remain unchangeable during its lifetime. The HUK serves as the foundational cryptographic key used for deriving the other secret keys in a system. To best protect the UID/HUK as well as other stored secrets in the HRoT, anti-tamper measures must be adequately designed in both physical layout and digital RTL.
A critical aspect of the Hardware Root of Trust is the entropy source to feed a device’s cryptographic algorithms. Therefore, a true random number generator (TRNG) should be employed to ensure the highest quality of entropy, instead of a using pseudo-random number generator (PRNG). A reliable dynamic entropy source (such as a TRNG) is essential for an HRoT for creating a secure operational environment. This protects the Secure Boot flow, provides comprehensive asset protection, and enhances the overall security of the system’s cryptographic functions.
