The complete hardware security solution.
A Crypto Coprocessor is a dedicated hardware module that accelerates cryptographic operations on a device and provides a reliable foundation to build a security sub-system on a chip.
They are embedded within an SoC and include multiple hardware security measures to protect the chip from reverse-engineering, physical tampering and supply chain counterfeiting threats. Crypto Coprocessors require the combination of both Hard Macros and Digital RTL IP to create a secure boundary for encryption-related processing. They offload symmetric operations from the main CPU that require cryptographic algorithms to help accelerate the encryption and decryption of data. This keeps all decrypted data within the secure boundary and removes the vulnerabilities associated with outputting decrypted data onto a bus.
Today, Crypto Coprocessors are already widely deployed in everything from missiles to smart cards. However, they are set to become an essential IP block in chip design as modern confidential computing standards require crypto coprocessors, such as TPM 2.0.
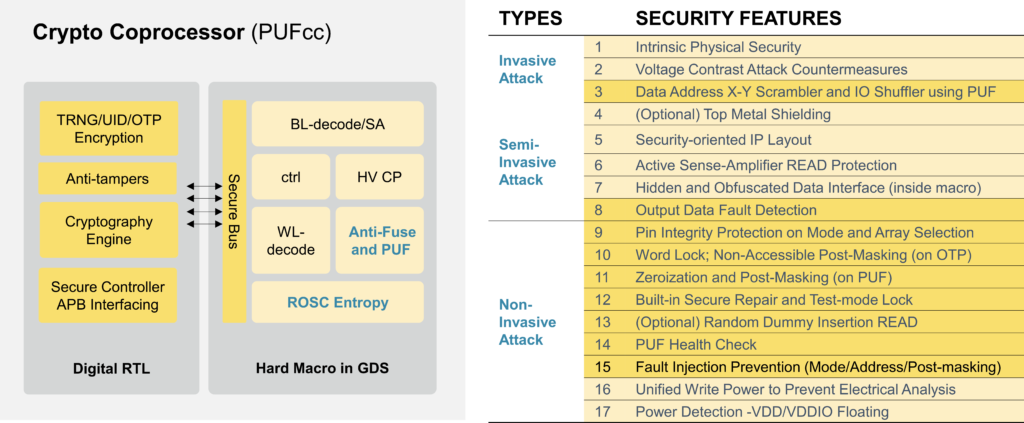
Crypto Coprocessors protect against a wide array of invasive, semi-invasive, and non-invasive attacks. They provide anti-tampering protection, detect and contain attacks, and the automatic zeroization of sensitive data. Crypto Coprocessors also establish a protected Hardware Root of Trust during the Secure Boot Loader phase. This authenticates the chip, the operating system, and all subsequent applications brought onto the device.
Want to learn more?
