Random Number Entropy
Algorithms that generate random numbers are vital in modern computing and play a role in everything from video games to secure internet browsing. We generally define two categorizations of random numbers, ”true” and ”pseudo.”
Pseudo-random numbers are not hardware-based (derived from a random physical process) and instead use, for example, a seed number and an algorithm to produce numbers that appear to be random. This is perfectly fine within a computer game but becomes an easily exploitable weak link when used for encryption and decryption.
Generic Structure
True Random Number Generators or TRNGs take this to the hardware level as a physical process. Typically, they generate random numbers from one or several entropy sources. This provides the “true” randomness from environmental noises or anything that operates with randomness in nature, such as the decay of a radioactive atom.
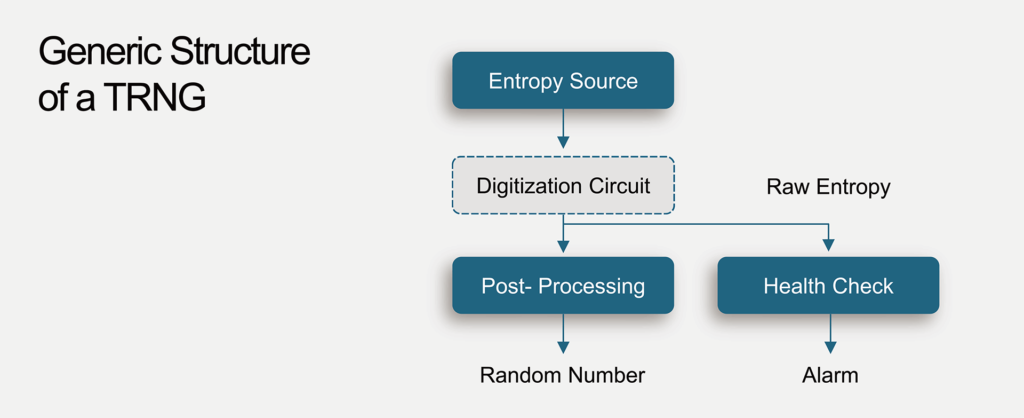
However, an entropy source is typically an analog signal due to practical limitations of digital semiconductor design. Therefore, a digitization circuit is necessary to sample the time-variant randomness of these entropy sources and convert the analog signal into digits for the modern CPU system. The digital signal sampled from the entropy source is called raw entropy. However, the raw entropy is not always ideally random. There may be some bias in the entropy sources or digitization circuit, which means the Hamming Weight (the ratio between the number of bit zero and bit one), may not be close to 50%. In other words, not perfectly random.
To improve the quality of raw entropy, we may need to post-processing to convert it into useable random numbers, such as using helper data. Alternatively, this process can be done from within the chip using a Quantum Tunneling PUF as an entropy source and removing the need for helper data.
Regulations
The security strength of many systems and applications depends on a high-quality RNG. The National Institute of Standards and Technology (NIST) has proposed in document NIST SP800- 90C the construction of a qualified RNG that combines true random number seeds, deterministic random bit generators, and post-processing algorithms. However, a true high-quality random seed is hard to design. An entropy source must provide ideal randomness and be derived from physical sources. Moreover, according to NIST regulations, four separate entropy sources are needed to construct a fully qualified true random number generator (TRNG).
Live seeds should be modified by an approved post-processing method before an application uses them to enhance security strength. The counter mode of the advanced encryption standard (AES-CTR) and hash (SHA2-256) function are the two post-processing algorithms used most frequently.
