Simpler, stronger authentication
Fast identity online (FIDO) authentication is a set of specifications defined by FIDO Alliance to reduce the amount of password-based authentication between users and cloud servers. FIDO is a device-centric model managing users’ information on distributed devices instead of the centralized management of personal account information on a cloud server. In addition, FIDO facilitates interoperability among devices by alleviating the management of multiple usernames and passwords over various cloud services.
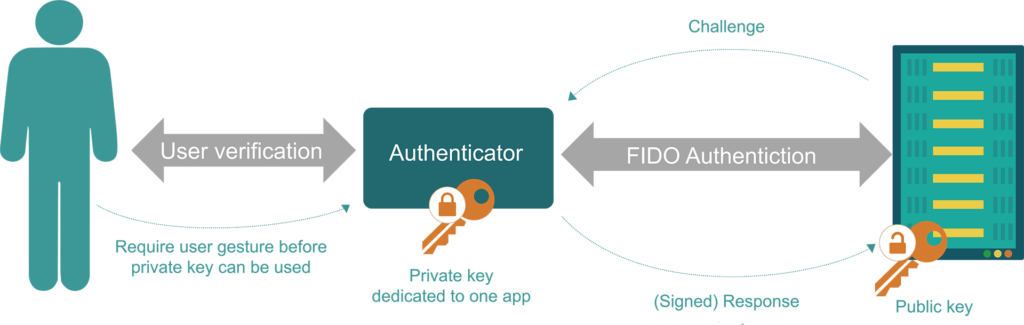
FIDO uses standard Public Key cryptography techniques to decentralize the authentication process. It uses a two-step procedure, i.e., authentication between a user and a user’s device and authentication between the user’s device and a cloud server.
The precondition of FIDO is that the user’s device must create a unique public/private key pair for the local device, cloud service, and user’s account during the registration stage. The user’s device first sends the public key to the server, and then the server associates the public key with the user’s account. Afterward, the user unlocks the private key every time the user gains access to the device through multiple forms of biometric authentication, e.g., fingerprint, voiceprint recorder, or face ID agreed in the registration stage.
The successful authentication between the user’s device and the cloud server relies on proving that the device possesses the private key through an effective response to a cryptographic challenge from the cloud server. As shown in the above figure, the user’s device signs the challenge from the cloud server by the private key. Then, the cloud server verifies the signed challenge by the stored public key. It is noteworthy that private keys and users’ information are never disclosed from the local user’s device. This is the main principle of FIDO to protect user privacy from the ground up.
FIDO provides simple, robust, device-centric authentication through biometric identification. They protect IoT users today and combat the increased risks in Key Management, both from user error and adversarial attacks.
